UP forms SIT to probe cases against Alt news co-founder Zubair | India News

NEW DELHI: The Uttar Pradesh government on Tuesday formed a Special Investigation…

NEW DELHI: The Uttar Pradesh government on Tuesday formed a Special Investigation…

WASHINGTON: President Joe Biden will host the first four-way virtual summit with…

The World Masters Athletics Championship was held in Tampere from June 29…

Ranbir Kapoor is opening up like never before and spilling the beans…
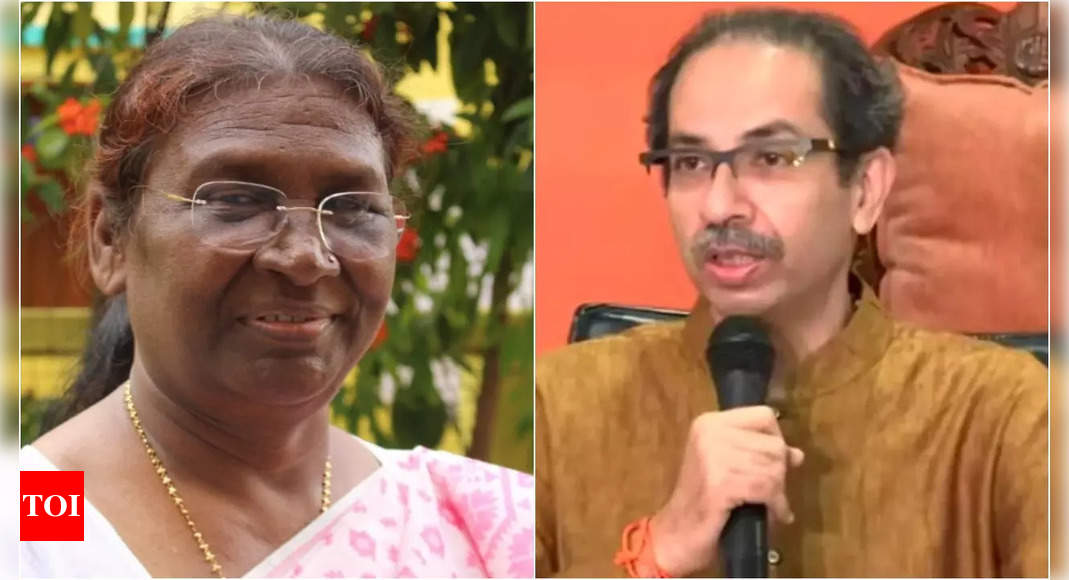
NEW DELHI: Shiv Sena supremo Uddhav Thackeray on Tuesday said his party…

After expressing their opposition to any kind of foreign support in terms…

MOSCOW: Russian President Vladimir Putin will visit Iran next week, the Kremlin…

British Television sensation Tommy Fury has lashed out at his father’s claims…

Adarsh bahu is a term that may sound old-fashioned but it’s the…

NEW DELHI: Congress leader Rahul Gandhi on Tuesday left for a “short…


